Trust & Security
Security is fundamental to RiskFortress. We employ zero-trust architecture, end-to-end encryption, and secure development practices to protect your data. Our enterprise GRC platform is designed with security-first principles and maintains compliance with SOC 2 Type II and ISO 27001 standards.
Zero-Trust Architecture
RiskFortress is built on zero-trust principles, ensuring that every component and user is verified and authorized.
- Identity-based access control with role-based permissions
- Least privilege access principles
- Continuous verification of user and system identities
- Network segmentation and micro-segmentation
- No implicit trust assumptions
- Comprehensive audit logging of all access
End-to-End Encryption
All data is encrypted at rest and in transit using industry-standard encryption algorithms.
- AES-256 encryption for data at rest
- TLS 1.3 for data in transit
- Encrypted database storage
- Encrypted backups and archives
- Key management with rotation policies
- Field-level encryption for sensitive data
Agent Security
Lightweight agents use secure communication protocols, signing, and attestation for enhanced security.
- Cryptographic signing of agent communications
- TPM-based agent security (when available)
- Secure agent-to-platform communication
- Agent attestation and integrity verification
- Memory protection mechanisms
- Secure credential storage and management
Signing & Attestation
All agent communications and data transfers are signed and attested to ensure integrity and authenticity.
- Digital signatures for all agent communications
- Code signing for agent binaries
- Attestation reports for compliance
- Integrity verification of data transfers
- Tamper detection and prevention
- Audit trail of all signatures
Compliance Posture
RiskFortress maintains its own compliance posture and undergoes regular security assessments.
- SOC 2 Type II compliance (in progress)
- ISO 27001 alignment
- Regular third-party security audits
- Penetration testing and vulnerability assessments
- Security incident response procedures
- Compliance with data protection regulations
Secure SDLC
Security is built into every stage of the software development lifecycle, from design to deployment.
- Security-first design principles
- Secure coding practices and standards
- Automated security testing in CI/CD
- Dependency vulnerability scanning
- Code review and security audits
- Regular security training for developers
Security in Practice
See how zero-trust architecture and security controls are implemented in RiskFortress.
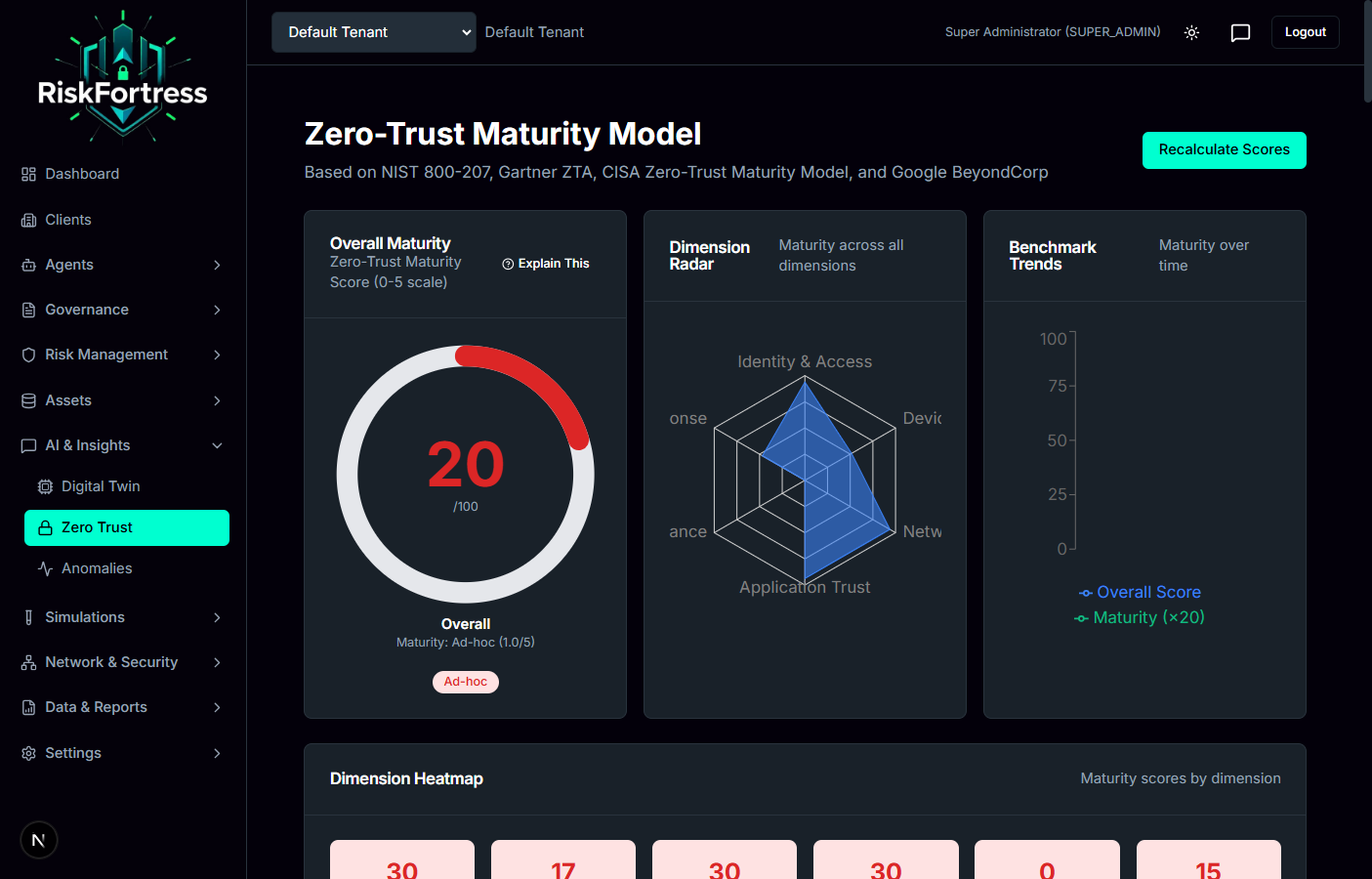
Zero-Trust Maturity Assessment
Comprehensive zero-trust architecture assessment across six dimensions
Security Audit Logs
Comprehensive audit logging and security event monitoring
Security Principles
Our security approach is based on industry best practices and defense-in-depth strategies.
Defense in Depth
Multiple layers of security controls to protect against various attack vectors.
Least Privilege
Users and systems are granted only the minimum permissions necessary for their functions.
Security by Design
Security considerations are integrated into every aspect of the platform from the ground up.
Data Protection & Privacy
We take data protection seriously and implement comprehensive measures to safeguard your information.
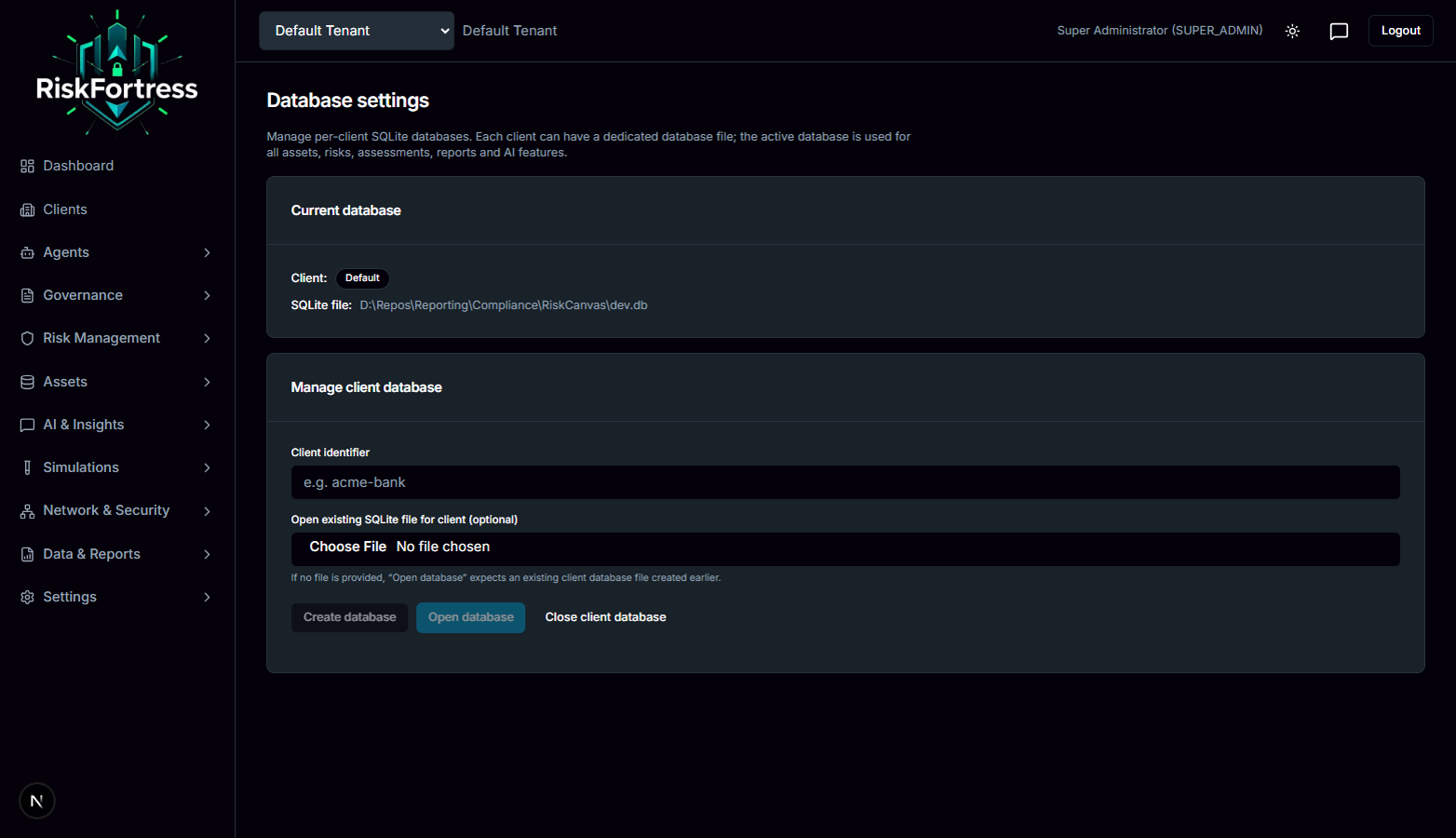
Data Residency
On-premise deployments ensure your data never leaves your infrastructure. For cloud deployments, we support data residency requirements and regional data storage options.
Data Retention
Configurable data retention policies allow you to control how long data is stored and when it is automatically purged according to your compliance requirements.
Access Controls
Granular role-based access controls ensure that users can only access data and functions appropriate to their role. Multi-factor authentication is supported for enhanced security.
Audit Logging
Comprehensive audit logs track all user actions, system events, and data access for compliance and security monitoring. Logs are tamper-proof and retained according to your policies.